Summary of results against reduced SHA-2 family. Effort is expressed as... | Download Scientific Diagram
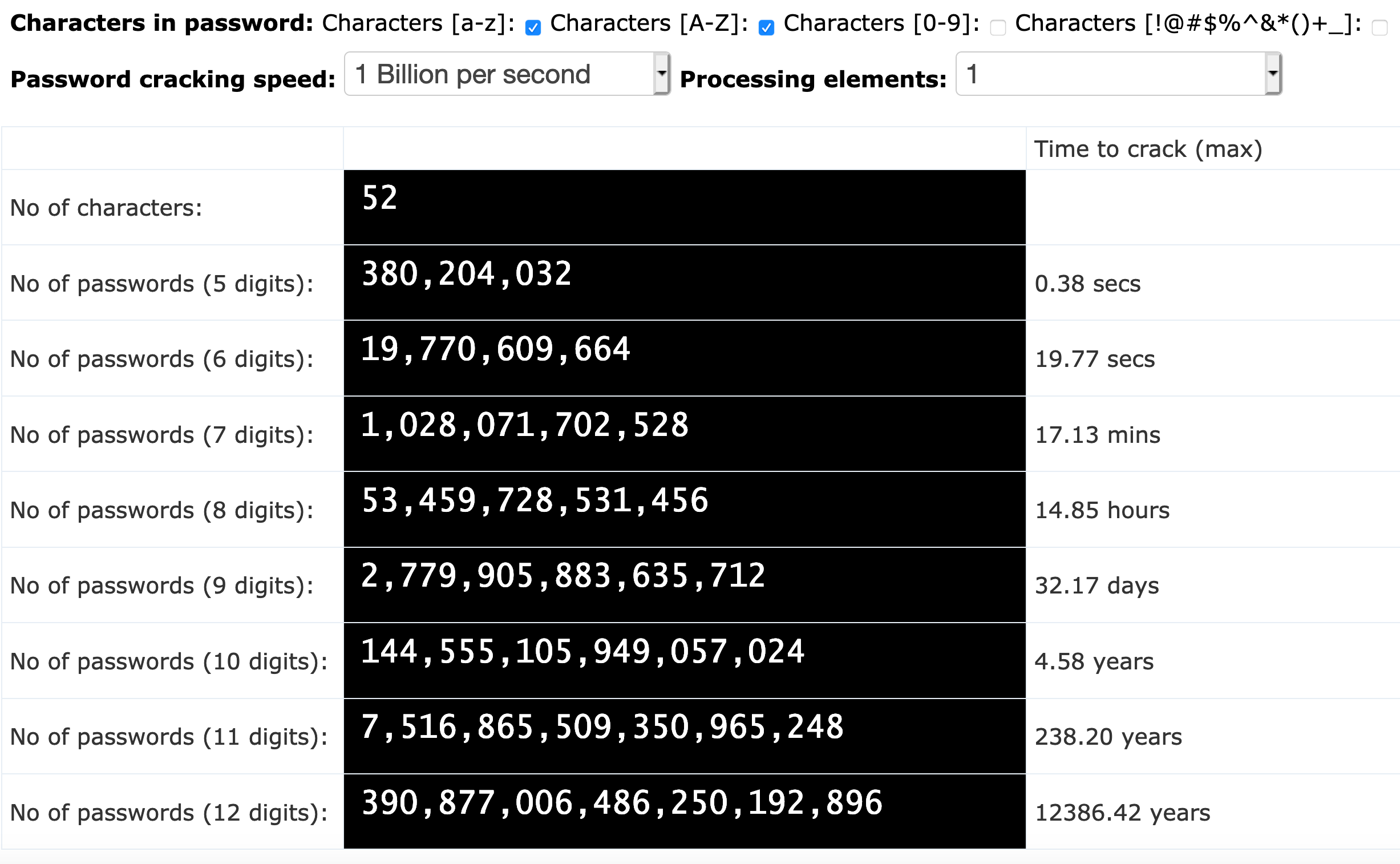
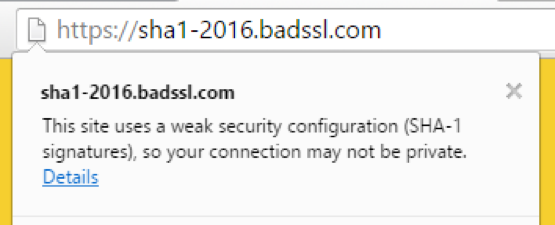
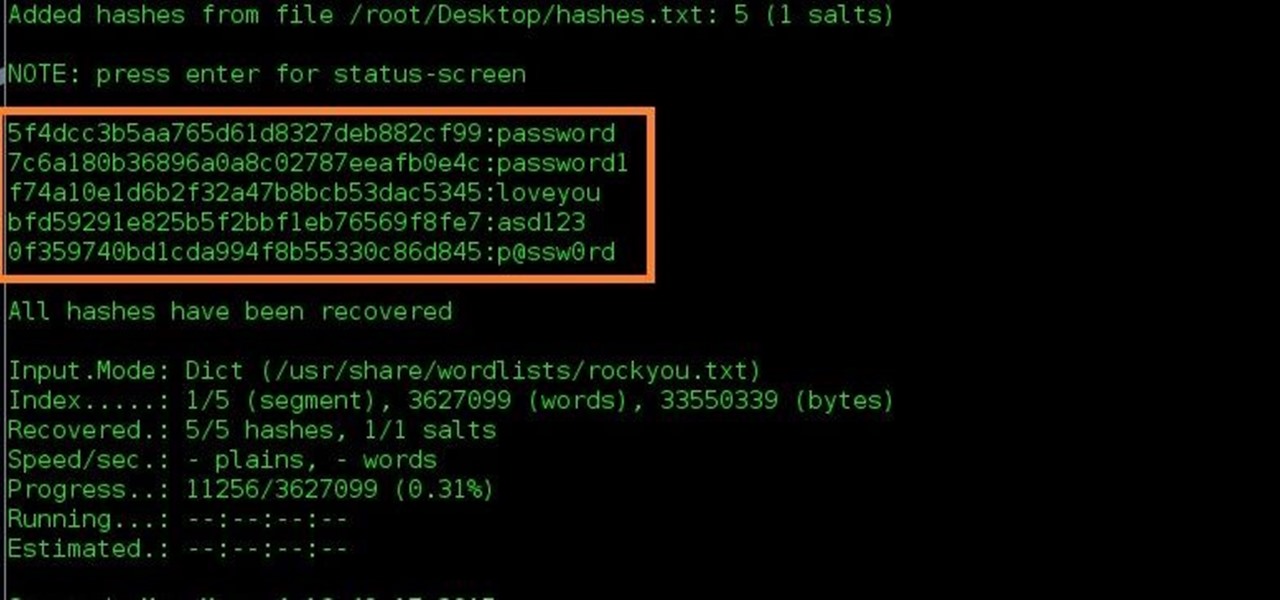
The Problem With Passwords…. A couple of comments I received… | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium

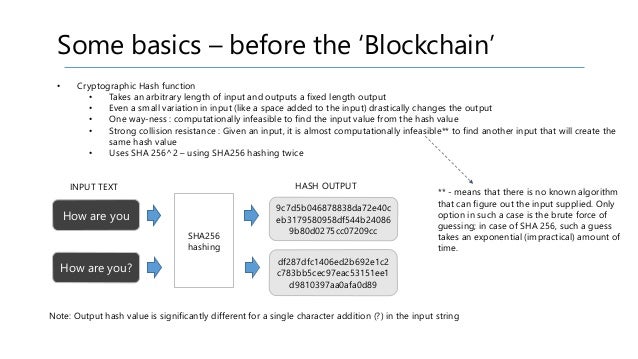
How Cryptographic Hash Functions Solve a Very Difficult and Important Problem | by Bennett Garner | Medium






![What Is Hashing? [Step-by-Step Guide-Under Hood Of Blockchain] What Is Hashing? [Step-by-Step Guide-Under Hood Of Blockchain]](https://i.ytimg.com/vi/IGSB9zoSx70/maxresdefault.jpg)