Cybersecurity: Internet security 101: Six ways hackers can attack you and how to stay safe - The Economic Times
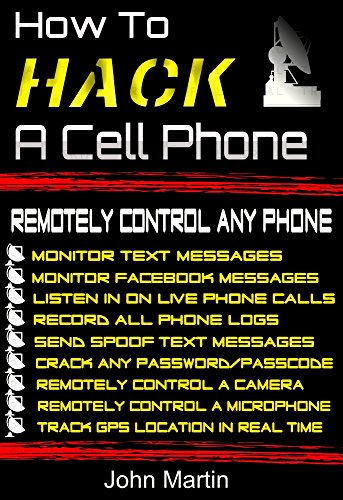
Amazon.com: How To Hack A Cell Phone: Remotely Control Any Cell Phone eBook : Martin, John: Kindle Store

Amazon.com: Saramonic SmartMic Mini Condenser Flexible Microphone for Smartphones,Vlogging Microphone for iPhone and YouTube Video, Mic for iOS Apple iPhone iPad and Android Phone : Electronics

Can an iPhone be hacked? A breakdown of common hacks and cyber hygiene best practices | McKelvey School of Engineering at Washington University in St. Louis